Wi-Fi de-authentication attacks and how you can prevent them using 802.11w or WPA3
TL; DR. Most of us today may have the perception that the use of Wi-Fi (IEEE 802.11) comes with an inherent risk; an attacker in close proximity could perform an attack which continuously disconnects a client from the Wi-Fi network. Such an attack is often termed as a non-persistent denial of service attack, as the victim device will regain access to the Wi-Fi network once the attacker stops the attack. However, do you know that the use of 802.11w or WPA3 standards can help to prevent such an attack from happening? To enable this feature, both the router and the client device have to support the standard.
Background
Today, the use of wireless technology could be ranging from products used in your smart homes, or even in life critical scenarios such as medical devices in hospital. Wi-Fi also known as wireless fidelity, brings convenience as it does not rely on traditional wired method to provide internet connectivity. As the Wi-Fi standards continue to evolve, consumers are enjoying faster upload & download speed.
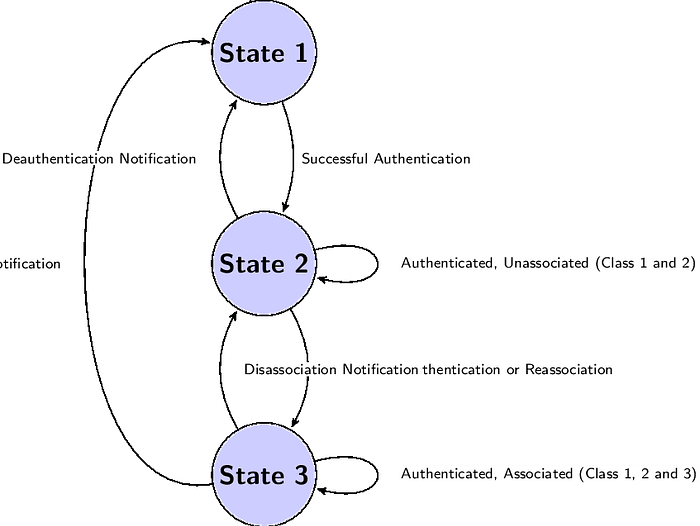
When your wireless enabled device attempt to connect to a Wi-Fi network, it will perform a series of exchanges to establish a connection. In order to achieve a successful connection between the device and the Access Point (AP), it has to be in state 3 as seen in Figure 1 below — an authenticated & associated state.
Why is de-authentication (a.k.a deauth) attacks dangerous?
As Wi-Fi uses the 2.4GHz and 5GHz frequency band of the radio spectrum, anyone in close proximity with the proper hardware gear could eavesdrop or transmit malicious packets on these band. In today’s Wi-Fi network, we can be assured that the data frames travelling in the air are often encrypted. Unlike the data frame, management frame which does the (de) authentication, (de) association, beacons and probes cannot be encrypted as these frames must be heard and understood by all clients. Because of that, an attacker could spoof Wi-Fi packets and send de-authentication packets to continuously disconnect a client device from a network.
De-authentication is a process to disconnect a client from the network, transiting from state 3 to state 1 in Figure 1. The de-authentication message can be triggered either by the AP or the client. For the former, when an AP has too many concurrent connections (approximately 250), the AP could send de-authentication messages to disconnect client devices which have been idle for a long period of time. For the latter, a client device could send a de-authentication message to indicate it is leaving the network.
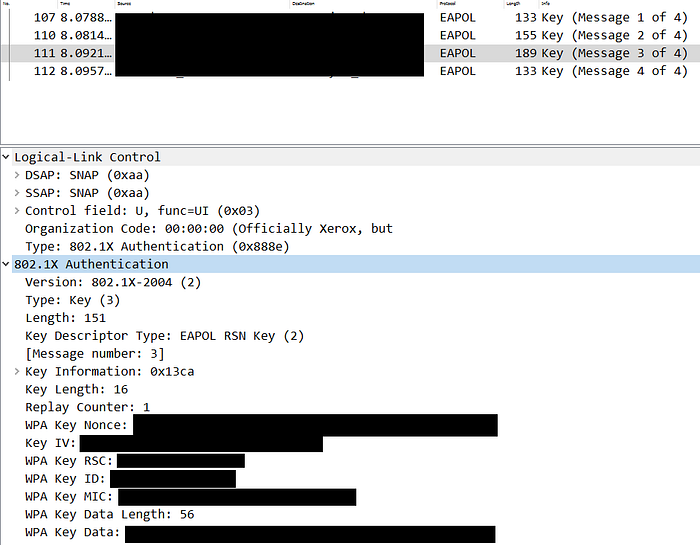
The key motivation on why an attacker will perform a de-authentication attack is to force the client to perform an authentication back to the network. By listening on the frequency, an attacker can capture the 4-way handshake between the client and the AP during authentication, and could then attempt to perform a brute force attack offline to obtain the network’s PSK. The 4-way handshake is basically a process to pass additional information to calculate the Pre Transient Key (PTK), which is used to encrypt uni-cast traffic.
To explain in greater detail on how the brute force attack works, it is essential to note that Wi-Fi uses multiple keys for its authentication process. When connecting to a Wi-Fi network, we often key in a password/passphrase, which is also known as the Pre Shared Key (PSK). The PSK is never sent on the network, instead, it is used as a variable along with other information to calculate the Pairwise Master Key (PMK) –> PBKDF2(passphrase, ssid, ssidlength, 4096, 256).
With knowledge of the PMK, the 4-way handshake then takes place to obtain the nonce and from the client and the AP. With the nonce and other information obtained from the ‘air’ (e.g. beacon etc.), the PTK can then be derived. PTK -> PRF (PMK,”Pairwise Key Expansion”, ANONCE, SNONCE, MAC of Client, MAC of AP).
In this article, I won’t be covering the techniques on how to perform the de-authentication attack. There are lots of great article out in the internet that gives a detailed walkthrough using the aircrack-ng tool. For completeness, below is a screenshot to depict what you will observe when the tool is performing the de-authentication attack. You will notice two de-authentication packets sent, one to the client, the other to the AP. (as mentioned earlier, de-authentication can be triggered by either parties).

All in all, if an attacker is able to crack the PSK (likely due to weak password reasons), he will then be able to gain a foothold into your internal network.
Is there anything we can do about the management frames?
Yes, use 802.11w or WPA3! Noting that the management frame could result in potential attacks, the 802.11w standard was published in 2008 to address the issue. Its key objective was to increase security by providing data confidentiality of management frames, mechanisms that enable data integrity, data origin authenticity, and replay protection. In WPA3, this feature is built in, however, it will likely take some time for (~10 years) all the products and devices to shift from WPA2 to WPA3. I have played with a Google Nest that supports WPA3, but upon enabling this new standard, some smart devices were unable to connect to the AP. In summary, both the 802.11w and WPA3 must be supported by both the AP and the client device.
How 802.11w/WPA3 works?
As mentioned earlier, management frames such as deauthentication, disassociation, beacons, and probes are always unauthenticated and unencrypted. With 802.11w/WPA3 enabled, the AP adds Message Integrity Check Information Element (MIC IE) to each management frame it transmits. This is achieved by introducing a new key called Integrity Group Temporal Key (IGTK), which is used to protect broadcast/multicast management frames. The key is derived during the four-way key handshake process. Any attempt to copy, alter, or replay the frame invalidates the MIC. In addition, some information in the management frame are encrypted.
How does it look like?
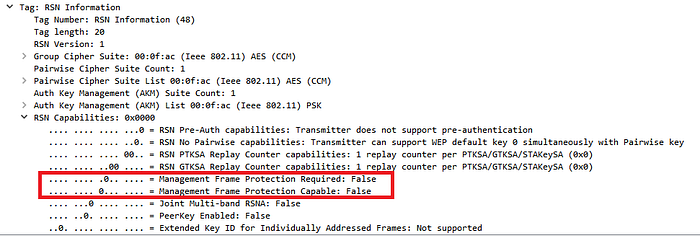
To determine if an AP supports management frame protection, simply head to any beacon packets and view the RSN capabilities. The box highlighted in red below shows two settings for management frame protection. If the required bit is set, any clients that wishes to connect to it needs to support Management Frame Protection (MFP) capabilities. If the capable bit is set, MFP is used if the client supports it.
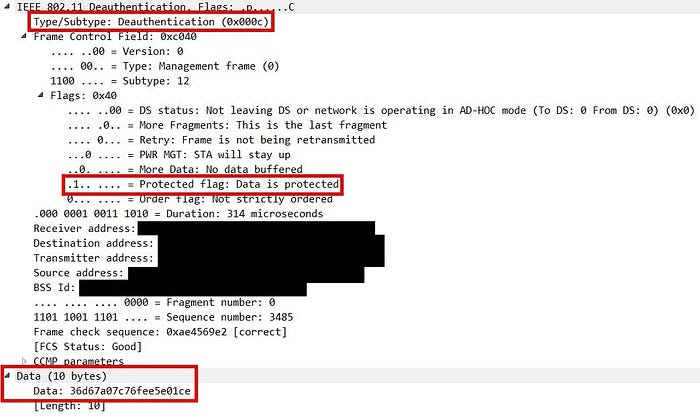
Let’s take a look at what the output will look like if MFP was in place when a de-authentication attack happens.

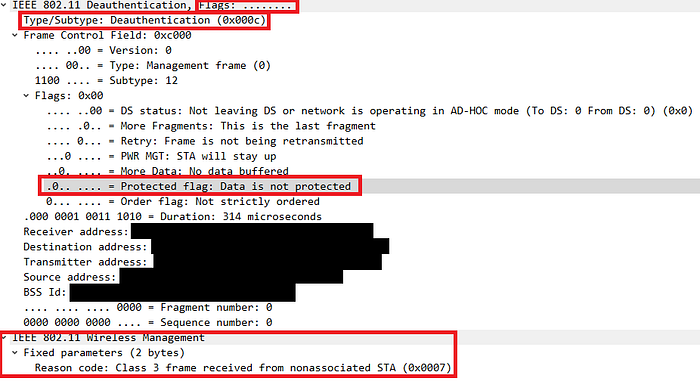
In Figure 6, it shows the detail of an attacker performing a de-authentication attack. We can pinpoint 2 issues. Firstly, the de-authentication frame is not protected. Secondly, the reason code is unencrypted. With MFP in place, the client or AP will just ignore the entire packet. Let’s take a look at a legitimate de-authentication packet from the AP.
Why isn’t WPA3 or 802.11w enabled and made available by default?
With the introduction of management frame protection in 2008, the question arises, why do the majority of APs today not support this feature? If it can help prevent such trivial attack, shouldn’t it be a default feature? Furthermore, MFP are only supported on higher end and more expensive (250 USD and above) router models today. I couldn’t find any answers on the Internet on why is 802.11w not a default standard today. My personal take suggests the following to be the potential reasons:
· It slows down the overall processing speed. There is an additional overhead if there is a need to encrypt or decrypt management frames all the times. I did a quick speed check against WPA2 and WPA3 on the Google Nest. The results showed that I had a greater download speed (approximately 20%) on the WPA2 standard. Wi-Fi was designed to bring about convenience, and speed is always its number one priority to consumers.
· De-authentication attacks are not a huge threat to consumers. It is not common to hear news on people reporting on one another for conducting de-authentication attack. Even if you lose connectivity frequently, will you spend time to actually verify if someone was actually attacking your network?
· Similar to the new WPA3 standard, it requires both the AP and the client to be able to support the standard. Likewise, when 802.11w was released, it could be that existing clients were unable to support it. Since the world didn’t have to rely on this feature (no world-wide concerns), it ended up becoming less important.
Tips on Wi-Fi security
· Use a long and complex password for your Wi-Fi PSK. Even though the WPA2 standard now requires a minimum of 8-character long password, consumers often put a simple dictionary word or just digits. Best recommendations for your PSK is to have a minimum length of 20 characters, and enforce sufficient complexity (special characters, upper/lowercase, numbers)
· Wi-Fi should never be used if your setup involves time or life critical use cases. In this article, we shared on only one denial-of-service attack with potential solution for it. However, there are still other forms of Wi-Fi attacks which are not covered (e.g. RTS/CTS, Channel Switching, resource starvation attack etc.). It is wise to evaluate the risk and likelihood of such attacks arising.
· Use 802.11w or WPA3 if supported. If this feature is made available to you, and doesn’t disrupt your environment operations, there is actually no harm enabling it. The key reason why attackers will perform de-authentication on your network is to attempt to obtain and crack your PSK and gain access to your network.
